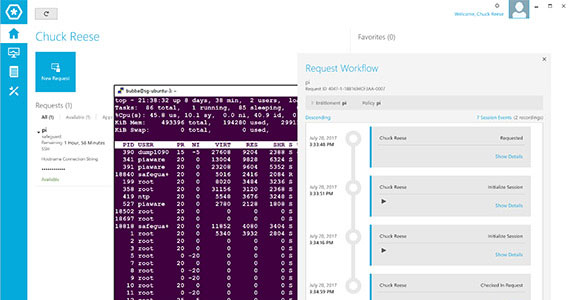
Safeguard for Privileged Sessions
Control, monitor and record privileged sessions of administrators, remote vendors and other high-risk users. Safeguard for Privileged Sessions protects against modern attacks and can disconnect questionable activity automatically. With its comprehensive, searchable session recording and reporting, it reduces stress about upcoming audits.
Key Benefits
Mitigate risk of breaches
Easily meet compliance needs for monitoring privileged access
Quick return on value with fast deployment and adoption
Happy admins with new capabilities on familiar tools
Features
Full session audit, recording and replay
All session activity is captured, indexed and stored for tamper-proof data trails
Real-time alerting and blocking
Monitors traffic in real time to catch and disconnect suspicious activity
Analytics ready
Collects all information to analyze privileged access and user behavior to detect threats
Full-text search
With built-in OCR engine, the auditors can search for any text typed or seen by the user
Work the way you want
Admins are free to choose their tools and clients, while keeping the organization compliant
Wide protocol support
You decide which protocols or network services to enable - SSH, Telnet, RDP, HTTPS, ICA, VNC etc
Privileged Access Governance
Unify governance so users can request, provision and attest to privileged and user access.
Resources
Safeguard for Privileged Sessions
Record and monitor privileged sessions to stop security threats in real time
Controlling and Managing Privileged Access
Effectively managing privileged accounts is critical to security and compliance efforts. Read this paper to learn the risk asso...
KuppingerCole Executive Review of One Identity Safeguard
KuppingerCole provides and overview of Privileged Management and then a review of One Identity Safeguard
Webinar: Regulating Privileged Access: When to Require Human Approval Workflows
View webinar to hear a discussion about risk factors and other situations that make human approval for privileged account acces...
Modernizing security: Proactive PAM solutions for today
One Identity Cloud PAM Essentials is a SaaS-based privileged access management (PAM) solution that prioritizes security, manage...
Understanding Privileged Identity Theft - Is your biggest threat inside your network
This ebook will explain why privileged identities pose such a risk to enterprises, how they are compromised by attackers, how c...
eBook: Strategies for successfully managing privileged accounts
One of the most important aspects of an identity security program is the management and governance of the accounts belonging to...
Privileged Access Management and DevOps: Integrating Security into the CI/CD Pipeline
Discover the cybersecurity challenges within the DevOps CI/CD pipeline and uncover effective solutions through the integration ...
