Identity Manager
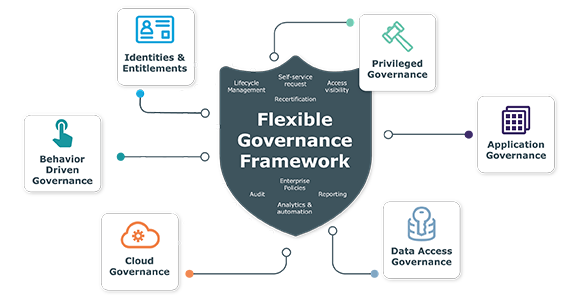
Identity Manager governs and secures your organization’s data and users, meets uptime requirements, reduces risk and satisfies compliance by giving users access to data and applications they need - and only what they need - whether on-premises, hybrid or in the cloud. Now, identity security can be driven by business needs, not by IT capabilities. With Identity Manager, you can unify security policies and satisfy governance needs — today and long into the future.
Key Benefits
Provide single platform for governance for users, data and privileged accounts
Extend governance to cloud apps
Unify policies to reduce risk exposure
Reduces risk by minimizing gaps in governance coverage
Satisfy compliance and audit requirements
Reduce helpdesk costs with automated enterprise provisioning
Industry recognition
Features
Identity lifecycle
Identity management software that secures user access and automates provisioning to any target on-premises or in the cloud.
Cloud
Extend identity governance beyond on-premises applications to hybrid and SaaS applications.
Governance
Single platform for governance for visibility to who has access to data and apps, when, how and why.
SAP Certified
Enhance existing SAP security models and connect accounts under governance. It’s true enterprise identity access management.
Attestation
Empower line-of-business personnel to approve or deny user and group access and entitlements.
Self-service access
Enable users to request entitlements and group access via a shopping-cart selection menu.
Privileged Access Governance
Unify governance so users can request, provision and attest to privileged and user access.
Compliance Reporting
Satisfy compliance regulations with user- and privileged-access reporting.
Application Governance
Streamline application-access decisions and enable line of-business managers to make decisions without IT input.
Integrations and Connectors
Extend identity governance capabilities to the cloud and reduce cloud application onboarding time.
Behavior-Driven Governance
Use access insights in OneLogin to inform governance policy decisions in
Identity Manager.
Resources
Identity Manager
Govern and secure user access to data and enterprise apps to reduce risk and satisfy compliance
Get comprehensive and certified SAP integration with Identity Manager
Read our technical brief to learn about our ongoing support and our latest SAP connector that extends our capabilities to the R...
Privilege Access Governance - Close the gap between privileged access and standard-user identiti...
With One Identity's Privileged Access Governance (PAG) module, have the capabilities of an identity governance (IGA) with priv...
The Journey to IAM Success: Exclusive insights and recommendations
Read this insightful overview of IAM-project strategy from KuppingerCole and One Identity to hear from organizations that have ...
How to Achieve HIPAA Security Compliance with Identity Governance and Access Management
In this paper, you’ll learn about IT security compliance for the Health Insurance Portability and Accountability Act (HIPAA) fr...
One Identity Manager celebrates its fifth anniversary at MTU Aero Engines
MTU Aero Engines uses the One Identity Manager to provide the ability to meet the constant growth in locations, employees, nece...
SAP GRC Framework Integration with One Identity Manager
SAP Cloud Identity Access Governance (SAP IAG) and SAP Access Control (SAP AC) are two powerful solutions from SAP to address c...
Successful integration with SAP solutions
On our mutual customers’ journey of cloud transformation, One Identity, as a partner of SAP, supports with their holistic ident...
Get started now
Mitigate risk, unify security policies, and satisfy governance and compliance needs with this identity management software.

