In my first and second blog posts in this series, I explained how limiting the power of user and admin accounts by controlling permissions and GPOs reduces the usefulness of those accounts to attackers — a key step in mitigating the insider threat. Now let’s focus on minimizing the ability of attackers to get control over those accounts in the first place.
Where do most attacks start? On user workstations. After all, they have far more interaction with the external world than admin consoles or servers; users are constantly using browsers, cloud applications and social media on their computers, while other endpoints may not even have an internet connection. Once attackers get a foothold on a user workstation, they look for credentials left there that they can take over, so they can move about in your network unnoticed. It’s bad enough if they get hold of end-user credentials left on a workstation— but it’s far worse if they manage to harvest admin credentials that grant more powerful privileges.
Therefore, it’s critical to closely control where admin credentials are used. One valuable technique is to use Microsoft’s Red Forest model: You put your admin accounts in three separate administrative forests, numbered 0–2. The most powerful accounts go in Tier 0, where you can more easily keep a close eye on them and apply more stringent security measures, such as requiring that they log on from a hardened workstation or complete a multifactor authentication (MFA) step.
Enterprise Reporter Suite makes it easy to assess the privileges of admin accounts to inform your Red Forest model, or to keep admins in check even if you don’t use that model. In particular, it will show you everyone who can log on to a particular workstation, so you can ensure that admins cannot leave credentials there for attackers to harvest. And Change Auditor can alert you if an admin attempts to log on to any vulnerable endpoint, with critical details such as the date and time and whether the attempt was successful, so you can wipe any credentials they might have left behind and update your policies to prevent them from logging on there in the future.
Okay, we’ve covered three practical steps you can take to dramatically reduce the insider threat:
- Understand and control privilege across the IT environment
- Control your Group Policy objects (GPOs)
- Keep admins in their lanes
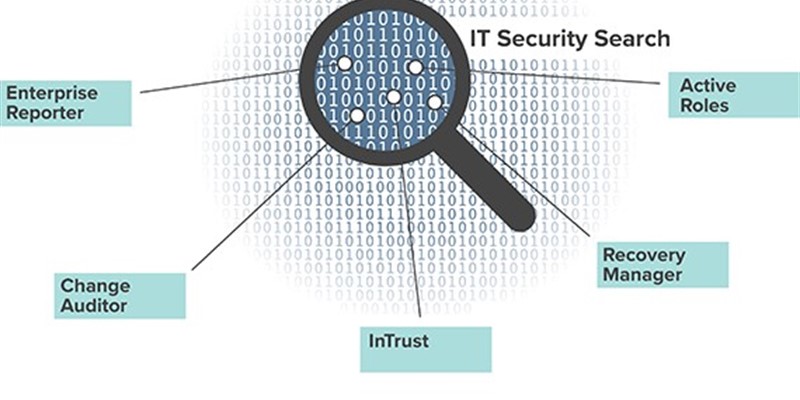
Fortunately, implementing these best practices does not have to mean three separate efforts — Quest also provides a solution that helps tie them all together: IT Security Search. IT Security Search is included free with Enterprise Reporter and Change Auditor, as well as several other Quest security and compliance solutions. It also works with GPOADmin because Change Auditor integrates fully with GPOADmin.
IT Security Search is a powerful search engine that enables IT administrators and security teams to quickly respond to security incidents and analyze event forensics. Its web-based interface correlates disparate IT data from multiple Quest security and compliance solutions into a single console. Starting from a simple, Google-like search, you can quickly uncover all the critical details of an incident — including details that native logs simply do not collect but Quest solutions do. For example, suppose Change Auditor alerts you to a change to a sensitive financial database. You can simply type the word “finance” into the IT Security Search search box and in minutes you’ll know which users, groups and workstations were involved and even the specific commands that were run on those workstations. With a single click, you can drill down into the details of a particular event, or pivot to see what else occurred on the workstations that a particular user touched.
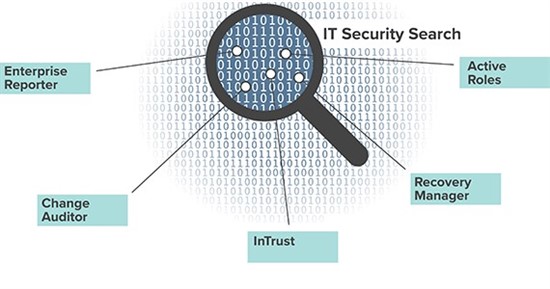
IT Security Search correlates disparate IT data from many Quest security and compliance solutions into a single console, facilitating analysis and quick incident response.
Mitigating the insider threat is essential for security, business continuity and compliance — in short, it’s critical to your business. Quest offers practical, proven solutions that make it much easier to carefully manage privileges, control GPOs and keep admins in their lanes. To learn more about these three best practices and the Quest solutions that help you implement them, check out our free ebook, “How to Mitigate the Insider Threat: Best Practices — and practical tools — for protecting your environment.”