-
Resources
- Forums
-
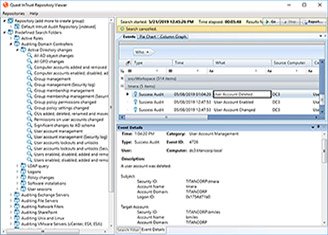
How to Sell More InTrust with Change Auditor
We are sorry, the event "How to Sell More InTrust with Change Auditor" has already expired.
You may also be interested in.

How to Improve your SIEM’s ROI and Threat-Hunting Potential
Are you getting maximum value from your SIEM? Probably not — 54 percent of cybersecurity pros say that their SIEM detects less than half of all security incidents, and many organizations have had to dial back monitoring to control SIEM costs. The root of the problem isn’t your SIEM. Most
Read White Paper
5 Best Practices for Endpoint Log Monitoring
Your organization’s data – and the users who have access to it – are only as secure as your endpoints, which are increasingly susceptible to cyberattacks. Workstation users, in particular, fall victim to drive-by downloads from websites they think they can trust, leading to ransomw
Watch Webcast
Key Issues to Consider in Endpoint Security
Watch this on-demand webcast and join security experts as they explore the need for better endpoint log management, which current solutions are not working, and how to achieve more robust endpoint security.
Watch Webcast
Integrated change auditing and event log management for strong security
This white paper explores how you can use Change Auditor and InTrust, either alone or in combination with your SIEM, to improve security and compliance while reducing costs.
Read White Paper
Quest Partner Webcast FY21 Q2 EMEA
Quest has the technology solutions your customers need to connect, manage and secure a remote workforce.
Watch Webcast
Quest Partner Update FY21
Recent events have forced governments to enact social distancing measures and business closures that have disrupted daily life and work.
Watch Webcast
Protect Your Active Directory from Ransomware using the NIST Cybersecurity Framework
Learn guidance on how to identify, protect, detect, respond to, and recover from ransomware cyberattacks.
Watch Webcast