IT Security Search
将不同的IT数据关联到交互搜索引擎。查看不可见的内容是IT面临的一项挑战。面对各种不同来源(内部部署和云环境中)中要收集和审核的数十亿计的事件,很难找到相关数据并了解其意义。在内部或外部出现安全违规时,能够确定最初发生违规的位置和访问的内容可以使局面大大改观。
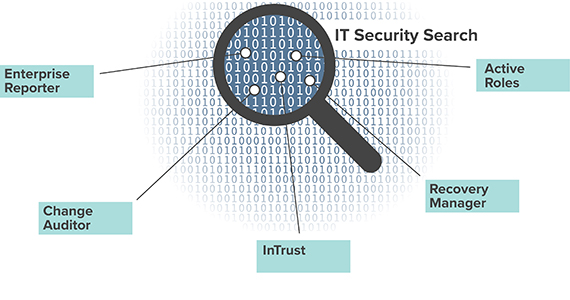
IT Security Search是类似于Google的IT搜索引擎,使IT管理员和安全团队可以快速响应安全事件和分析事件取证。该工具基于Web的界面将来自许多Quest安全与合规性解决方案的分散IT数据关联在单个控制台中,并且可以比以往更轻松地实现以下优势:
- 简化对分散在信息孤岛中的关键IT数据的搜索、分析和维护工作
- 通过全面的实时可见性,加速安全调查和合规性审计
- 在发生中断或安全违规时,对普遍存在的问题进行故障排除
- 配置基于角色的访问,使审核人员、服务台员工、IT经理和其他利益相关方可以准确获得所需的报告
功能
IT Security Search在多款Quest解决方案(包括Enterprise Reporter、Change Auditor、InTrust、Recovery Manager for AD和Active Roles)中都有提供,它可以提取数据并将数据馈送到单一窗格中。在此窗格中,您可以轻松审核您的内部部署或混合环境中的所有不同活动,并对其执行相应的操作。
基于状态的数据
- 通过Enterprise Reporter,可深入了解内部部署、Azure和混合环境中的以下方面的重要信息:用户、计算机和组,直接和嵌套组成员关系,OU和文件/文件夹权限,所有者等等。提高IT团队的能力,以全面了解其安全状态。
- 通过Active Roles查看虚拟属性、动态组成员、临时组成员和托管设备
实时安全审核
- 通过Change Auditor,搜索有关内部部署环境或Office 365和Azure Active Directory (AD)中重要对象和敏感数据更改的实时信息。
- 在本机审核详细信息中补充发起AD更改的实际用户信息,即使更改是通过Active Roles发起的也是如此
收集和存档日志
经过压缩且编制了索引的在线存储库
对象恢复
规格
- 兼容性
以下版本的数据提供系统在此版本的IT Security Search中受支持:
- InTrust 11.4.1、11.4、11.3.2、11.3.1、11.3
- Change Auditor 7.1、7.0.4、7.0.3、7.0.2、7.0.1、7.0、6.9.5、6.9.4、6.9.3、6.9.2、6.9.1、6.9
- Enterprise Reporter 3.2.1、3.2、3.1、3.0
- Recovery Manager for Active Directory 10.1、10.0.1、10.0、9.0.1、9.0、8.8.1
- Active Roles 7.4.1、7.4、7.3.2、7.3.1、7.2.1、7.2、7.1
- 软件要求
- 操作系统:
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012 R2
- Microsoft Windows Server 2012
- Microsoft Windows Server 2008 R2
- 其他软件:
- Microsoft .NET Framework 4.7.2或更高版本
- Microsoft Windows PowerShell 3.0或更高版本
- Microsoft SQL Server 2012或更高版本(所有版本)。这是IT Security Search Warehouse组件的要求,其需要这些内容进行内部配置管理。
Recovery Manager for Active Directory连接器的其他要求:
- 在Windows PowerShell中启用远程命令。有关详细信息,请访问https://technet.microsoft.com/en-us/magazine/ff700227.aspx。
- PowerShell脚本执行策略必须设置为RemoteSigned。运行以下 cmdlet:Set-ExecutionPolicy RemoteSigned
Active Roles连接器的其他要求:
- Active Roles管理工具
- PowerShell脚本执行策略必须设置为RemoteSigned。
- 操作系统:
- 浏览器兼容性
IT Security Search Web界面可以与以下浏览器一起正常使用:
- Microsoft Edge
- Microsoft Internet Explorer 11或更高版本
- Google Chrome 72.0或更高版本
- Mozilla Firefox 65.0或更高版本
支持的最低显示器分辨率为1024 x 768。
- 硬件要求
- CPU:最少6个核心;建议16个核心
- RAM:最少8 GB;建议16 GB或更多
- 磁盘:200 GB(建议使用SSD);磁盘空间要求与处理的Enterprise Reporter数据量紧密相关,因为索引大小按比例变化;Change Auditor和InTrust数据的索引不会占用IT Security Search计算机上的任何磁盘空间,因为它们都位于这些系统使用的数据存储中
- 如果您在虚拟机上部署,请确保满足上述CPU和内存要求,并且不会使虚拟机主机过载
要了解有关IT Security Search安装的磁盘要求,请参阅IT Security Search支持页面。 IT Security Search支持页面。
