InTrust
事件日志管理软件。贵公司最宝贵的资产是数据和对其有访问权限的用户,但是,您的安全取决于用户工作站。收集、存储和分析所有用户以及特权帐户数据通常需要大量存储、耗时地收集事件数据,以及关于所收集的事件日志数据的内部专业知识。这是我们可以提供帮助的领域。
Quest InTrust是可扩展的智能事件日志管理软件,使您可以监控所有用户工作站和管理员活动,从登录到注销以及其间的一切活动都包括在内。通过20:1的数据压缩削减存储成本,并存储来自Windows、UNIX/Linux服务器、数据库、应用程序和网络设备的长达数年之久的事件日志。InTrust实时日志监控和警报功能通过自动响应可疑活动,使您可以即时应对威胁。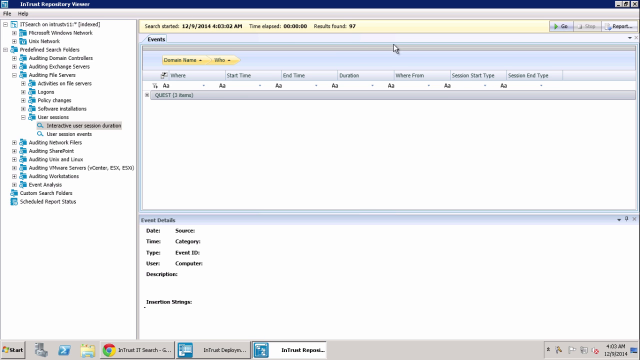 07:08
07:08
20:1
数据压缩
6万
个事件/秒
60%
的存储成本节省
其他功能
用户工作站日志监控
通过监控用户和管理员活动,从登录到注销以及其间发生的一切都包括在内,从而保护您的工作站以抵御现代网络攻击,例如哈希传递、网络钓鱼或勒索软件。收集并存储用户访问的所有重要详细信息,如谁执行了操作、该操作涉及什么、执行于哪一台服务器以及源于哪一台工作站。
超可扩展性
一台InTrust服务器每秒可以处理多达60,000个事件且支持10,000个或更多代理程序同时写入事件日志,使您实现更高的效率、更大的可扩展性和巨大的硬件成本节省。对于需要更多容量的大型企业组织,只需添加其他InTrust服务器并划分工作负载 - 可扩展性几乎是无限的。
通过IT Security Search提高洞察力
在一个位置便可利用所有Quest安全与合规性解决方案提供的宝贵洞察力。借助IT Security Search,您可以在一个响应快速的、类似于Google的IT搜索引擎中关联来自InTrust、Change Auditor、Enterprise Reporter、Recovery Manager for AD以及Active Roles的数据,实现更快的安全事件响应和取证分析。通过丰富的可视化和事件时间表轻松分析用户授权和活动、事件趋势、可疑模式等。
自动化妥善做法报告
轻松将调查结果转换为多种报告格式,包括HTML、XML、PDF、CSV和TXT以及Microsoft Word、Visio和Excel。借助内置的事件日志专业技术,安排报告的生成时间并自动将其分发给各团队,或从内容丰富的预定义妥善做法报告库中进行选择。通过数据导入和整合工作流,您甚至可以将数据的子集自动转发到SQL Server以进行进一步的高级分析。
防篡改日志
通过在可对创建的日志进行重复数据删除的每台远程服务器上创建缓存位置,保护事件日志数据,以防止篡改或销毁。
规格
- x64
默认安装的组件为InTrust Deployment Manager、InTrust Server和InTrust Repository Viewer。如果您自定义选择以安装各个组件,请参阅产品下载中提供的“InTrust系统要求”文档中所需组件的要求。如果您使用默认选择,则组合要求如下:
体系结构- 操作系统
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012 R2
- Microsoft Windows Server 2012
- CPU
最少4核(例如,用于评估目的)。
对于任何实际使用,建议至少8核。
- 内存
最低4 GB(例如,用于评估目的)。
对于任何实际使用,建议至少8 GB。*
- 其他软件和服务
- 具有所有最新更新的Microsoft .NET Framework 4.6.2或更高版本
- Microsoft SQL Server Native Client 11.0.6538.0或更高版本(客户端可重新分发包版本11.0.6538.0包含在InTrust分发版中)。重要提示:请提前安装所需的客户端版本,然后才能安装InTrust。
- 在虚拟化的环境中
如果您在虚拟机上部署InTrust,请确保满足上述CPU和内存要求,并且不要使虚拟机主机过载。
- 对于配置数据库:
- Microsoft SQL Server 2019
- Microsoft SQL Server 2017
- Microsoft SQL Server 2016
- Microsoft SQL Server 2014
- Microsoft SQL Server 2012
