Join IAM experts and your peers at Infosecurity Europe 2024, 4-6 June, in London!
Infosecurity Europe is your gateway to the entire information security community, connecting you with experts, engineers, innovators and industry leaders. Stay ah...
- Products
- View all products
- Free trials
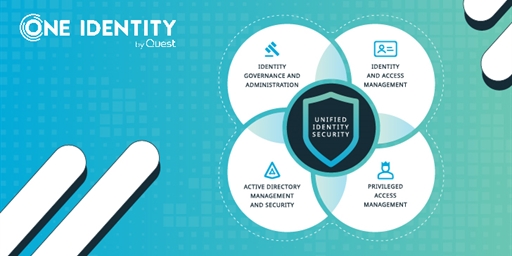
- Privileged Access Management
- Overview
- PAM Essentials
- Safeguard
- Safeguard On Demand
- Safeguard for Privileged Analytics
- Safeguard for Privileged Passwords
- Safeguard for Privileged Sessions
- Safeguard Remote Access
-
Endpoint Privilege Management
- Privilege Manager for Windows
- Privilege Manager for Unix
- Safeguard Authentication Services
- Safeguard for Sudo
- Access Management
- Identity Governance and Administration
- Active Directory Management
- Log Management
- Solutions
- Resources
- Trials
- Support
- Partners
- Communities