Welcome. This is KACE on the Go, a vlog series on trending topics and KACE solutions. Are you struggling to keep track of your IT assets and make sure they're updated and secure, even when they're remote? Are you ready for the next cybersecurity attack? Are you leaving your data center behind and moving to the cloud? You're not alone. Welcome to the KACE on the Go vlog.
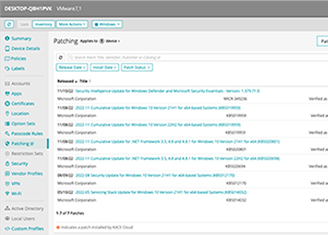
All right. So hey, welcome back to another edition of KACE on the Go. Today, we're going to be talking about the impact of unpatched applications in end-of-life software. And obviously everybody knows that that's a problem, but what we want to explore is maybe some of the things people might not think about as relates to that.
So my name is James Rico. I also have Jillian Salamon and Dave Hunter with us. We're all KACE sales engineers. So with that, I'll pitch it over to Jillian. And Jillian, what do you have to say about that?
Yeah, so one of the things I love most about my job is the conversations I get to have with such a wide variety of IT departments. The other day, I was speaking with a gentleman, and he is in the higher ed space. And the hospital that is affiliated with the school was actually hit with ransomware. And, unfortunately, this wasn't the first time.
So he had mentioned to me that he was out riding his bike, and I think it was, like, extreme bike riding-- ends up in a very bad accident. And just so happens he goes to the ER of the hospital that, at the same time, is having the breach, which I thought was kind of interesting.
So he was explaining how all elective surgeries had to be canceled for the day. Any emergency surgeries were actually-- they were shipping those patients out to different hospitals in the area. And yeah, so he did make me laugh. He said that there were nurses that were making rounds to take vitals of the patients, and it was complete mayhem.
They didn't know what they were doing because they didn't know how to manually take those vitals. So I think we become so dependent on technology that, when it's not available, our brain doesn't know how to react. But yeah, all of this could have been avoided if he actually just upgraded his virtual environment.
Wow. So do you know what the particular breach was that affected them?
Yeah I believe it was called ESXiArgs, if I'm pronouncing it correctly. But when I look at the CVE, it's really just-- any customers who were running version 6.7 were vulnerable. And they just needed to upgrade to version 7, and that removed that vulnerability.
Wow. Yeah, I think, a lot of times, just patching things is really a good first step into keeping things up to date, obviously. So that's good one. Dave, what about you? What experiences have you had?
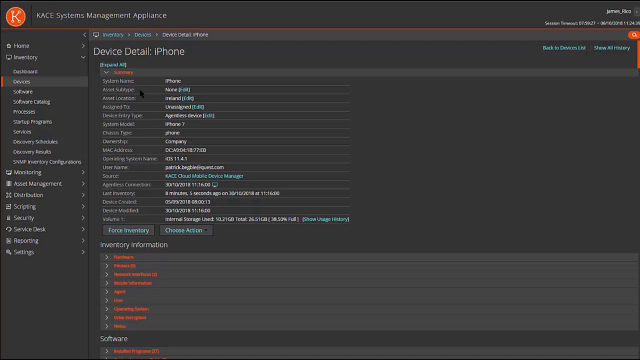
Yeah, obviously, like Jillian, we talk to different IT groups and people all the time-- different internal skill sets or budgets, and everyone's got some restraints. The one that comes to mind isn't really about patching per se, but it's around just best practices around security and mobility products.
So I had something pretty close to home that, when COVID kicked off-- everyone's reactive. I don't think there was any bad actors. Everyone was just trying really hard to keep businesses afloat.
So an individual did a bunch of payroll from their mobility device, and this corporation didn't have a mobility tool in place. So whether it was jailbroken or whatever it may have been, and then-- so long story short, there was some malware on a device. And in turn, a large portion of customer, employee data was compromised.
So once again, it's something that is avoidable. Company then has to pay for X amount of years of credit or protection and things like that to their employees. Which even still isn't great because that employee could be threatened years away from now, right?
But once again, people are trying to just do the right thing, keep the business afloat. So we see that quite a lot, I think, now that companies are trying to loop back around and catch up to what they had to do a couple of years ago. Some of them are paying the price.
Yeah. I don't know about you, but when I talk to people, like, if we're talking about patching or whatever, a lot of times, I'll ask them, it's like, hey, do you guys have-- do your employees have mobile devices they access company data with? And almost everybody-- like, I haven't had anybody say no. Like, the second question is, what do you guys-- do you have any controls around it? Do you manage that? And the percentage of people that do is very small. Has that been your experience, also?
Yeah. I mean I used to manage production environments before and it's shocking to me that they don't even have basics, like passcode security, on a device that has access to corporate data, at a minimum. So we see that all the time. It's actually very surprising. I'm actually shocked half the time that people in IT keep their jobs half the time when you have a look at their environments and how insecure or out-of-date products are.
Yeah. Just thinking, when I'm looking at the issue, I think one of the biggest things I think about is those companies that have a handle on the easy things, like their servers and their Windows desktops. Or maybe, let's say they even do have a mobile device thing. Like, how many of those shops have some kiosk or signage embedded PC hooked to something that is just running all the time and nobody messes with?
Or some kind of kiosk device-- one is, with the-- people change jobs so frequently now. There's those kind of devices out there, and also, the whole IT staff has changed over a year or two. And then there's things that people just don't know about. And if you don't know about them-- even if they're maybe an older OS or something, if they know about them, they can take care of it. There's ways to remediate. I think that's one thing.
The other thing, just kind of a little story, was, I knew a customer that was working for a bank organization that had a lot of branches all over the place. Well, they're running ATM machines with Windows XP Embedded. This is about 10 years ago, so that was not unheard of.
But he tried to do the right thing and just patch those. Well, he didn't test or validate or anything ahead of time. I don't know how many hundreds of ATM machines he broke. So sometimes, also, you can be your own worst enemy around that stuff. It's maybe not a breach, but you always need to think about testing and doing things like that.
It's interesting that you bring up the whole asset inventory thing. We come across customers that have great tools in place. They're doing everything they can. But they just lack asset management, or they lack good inventory control. So as you said, it just takes that one laptop that you refresh for someone. And they're like, hey, can I just keep my laptop for a couple of weeks to make sure I have everything? That week turns into a month turns into six months. And before you know it, it's back on the network, and it's vulnerable.
There's always that guy who has three laptops, for some reason, at your company. It's like, where did those come from? How do you still have all those? But yeah, I'm 100% with you.
Well, that, and if you think about not only an attack or a breach or something like that, but if you don't have a good asset management plan in play-- maybe, like you said, somebody's trying to be helpful. They have some software they think they need. They download it, put it on their work computer, and then you get an audit.
And if you don't know what's on your work computers, that could be a problem. They don't care-- you know, Microsoft or whoever, they don't care who puts the software on there. They just see it there, and they're wanting you to write them a check. So I really think that that ties nicely along with the conversation we're having today.
So to keep it moving along, Jillian, can you tell us a little bit how we use KACE here at Quest?
Yes. So we do actually drink our own champagne.
Champagne, eh?
That's right. We use KACE internally, obviously, to manage our endpoints. And I can remember, a couple of years ago, getting this urgent email that said, any lab environments that were out there, they were required to have the KACE agent installed on them. Because they wanted to ensure know those devices were getting critical security updates.
When you think about Quest, think of all the different products that we have and all the testing that needs to be done. So I was just curious to see how many labs we actually had under management, and it's 8,881 devices. So I was kind of shocked at that number.
It's just growing, too.
Yeah, exactly.
It's probably increasing. I don't think people think about that, though. That's a great point. Like, how many companies-- they handle their standard stuff, and then you have these labs, computer labs, if they're in software sales at all. I mean, those are patched or updated or even inventoried.
Exactly. What's also kind of cool is they actually use KACE to deploy a script that will record who owns that lab device so that, if there is some type of breach, they know who to contact. And they can act quickly if they need to power down the machine or something like that. That's definitely a proactive approach, and probably the right approach, to be honest. So kudos to our IT department for being so proactive.
Yeah. And those threat actors, they don't care if it's a lab machine or production or whatever. They're just looking for that foot in the door to get things going. So great. Yeah. I really didn't think about that, either. I mean, you brought this up and was telling me about it. And I was like, yeah, that makes a lot of sense. We really need to keep an eye on that.
All right. Well, we've been going on for a bit here. Dave, we'll let you have the last word. Wrap us up today.
Oh, thanks, man. Yeah, yeah. So [INAUDIBLE] with Quest KACE, the family of KACE products, we've got a few things that can definitely help people. We've got the traditional systems management appliance, on-prem-hosted Azure kind of thing, which will take care of patch and mobile and inventory management.
We also have KACE Cloud Secure, which is being developed very aggressively. So that's really a Mac iOS, Android, Windows-based, subscription-based model which can patch and do everything out of Azure.
And I think the other part that sometimes people overlook is imaging, right? We still have a systems deployment appliance. So the ability to rapidly reimage and remove products that are infected from the environment-- there's one thing about being proactive. But when you do get hit, how can you maintain the business, reimage rapidly, and keep moving forward?
So definitely have a bunch of things we can help you with. You've got the three of us and our team behind us somewhere. We're here to help you guys and really make it a positive experience.
Great. Good talk. Dave, Jillian, appreciate you coming in today. Thanks, everybody. Visit us at quest.com/kace.
[MUSIC PLAYING]
 11:55
11:55