Hi In this demo, we're going to show you how you can minimize the impact of attacks based on PowerShell scripts, mainly so-called pass the hash attacks. What we are about to do is set up alerts and emergency response actions for whenever someone uses phishing PowerShell commands. We're going to use this rule, Suspicious PowerShell Activity, applied through this policy, past the hash activity.
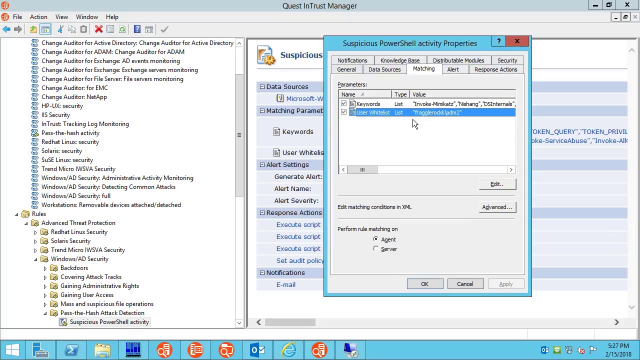
Have a look at the matching parameters. These are the potentially dangerous keywords that you want to watch out for. Keywords like this are typically found in modules that uncover system vulnerabilities, such as PowerSploit. These modules are often designed for testing purposes, but they can land in the wrong hands. We're not just catching the input at the command prompt. We break the activity down to the individual commandlets and parameters used in the process.
This is a wide list of users that you trust with PowerShell. When [INAUDIBLE] detects what looks like an attack, the rule disables the user account that's caught in the act, forcefully logs them off, stops the Windows Remote Management Service, and turns on emergency auditing.
Lets start a PowerShell session on a remote computer. The session will come in later. Let's play around as a whitelisted user on that same computer and simulate a successful attack. We're going to run some blacklisted commands.
Find a likely administrative account and get its credentials. Confirm that it really is an administrator. Get the name of a DC and log onto it. We're now in possession of the domain controller, scary stuff. As you can see, it only takes seconds to become all-powerful if you're prepared.
Now let's try the same tricks with a user that isn't whitelisted. We've been locked out, kicked off the computer and out of the PowerShell session.
Here's the email notification with the details. It includes an IT security search link, which can help you make sense of the situation. Remember that to make the defense work, you need to make sure PowerShell login is enabled for group policy. Thanks for watching.
 03:42
03:42
