InTrust
Event log management software. Your organization’s most valuable asset is its data and the users who have access to it — but you’re only as secure as your user workstations. Collecting, storing and analyzing all user and privileged account data generally requires large amounts of storage, time-consuming collection of event data and in-house expertise about the event log data collected. That’s where we come in.
Quest InTrust is smart, scalable event log management software that lets you monitor all user workstation and administrator activity from logons to logoffs and everything in between. Slash storage costs with 20:1 data compression, and store years of event logs from Windows, UNIX/Linux servers, databases, applications and network devices. InTrust real-time log monitoring and alerting enables you to immediately respond to threats with automated responses to suspicious activity.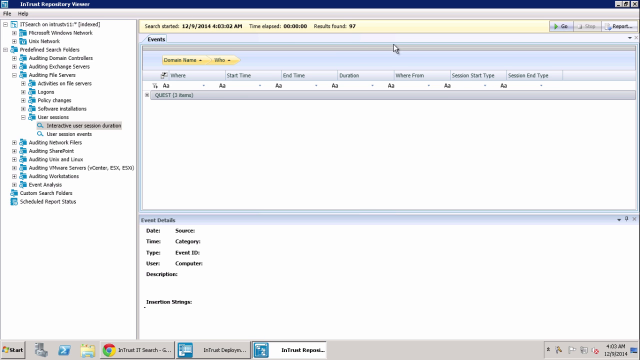 07:08
07:08
20:1
Data compression
60K
Events per second
60%
Storage cost savings
How much data are you sending to SIEM?
Additional features
User workstation log monitoring
Protect your workstations from modern cyberattacks, such as pass-the-hash, phishing or ransomware, by monitoring user and administrator activity — from logons to logoffs and everything in between. Collect and store all essential details of user access, such as who performed the action, what that action entailed, on which server it happened and from which workstation it originated.
Hyper scalability
One InTrust server can process up to 60,000 events per second with 10,000 agents or more writing event logs simultaneously, giving you more efficiency, scalability and substantial hardware cost savings. And for large, enterprise organizations who need more volume, you can simply add another InTrust server and divide the workload — scalability is virtually limitless.
Improved insights with IT Security Search
Leverage the valuable insights from all of your Quest security and compliance solutions in one place. With IT Security Search, you can correlate data from InTrust, Change Auditor, Enterprise Reporter, Recovery Manager for AD, and Active Roles in a responsive Google-like, IT search engine for faster security incident response and forensic analysis. Easily analyze user entitlements and activity, event trends, suspicious patterns and more with rich visualizations and event timelines.
Automated best practice reporting
Easily convert investigations into multiple report formats, including HTML, XML, PDF, CSV and TXT, as well as Microsoft Word, Visio and Excel. Schedule reports and automate distribution across teams or choose from a vast library of predefined best practice reports with built-in event log expertise. With data import and consolidation workflows, you can even automatically forward a subset of data to SQL Server for further advanced analysis.
Tamper-proof logs
Protect event log data from tampering or destruction by creating a cached location on each remote server where logs can be duplicated as they are created.
Specifications
- x64
The components installed by default are InTrust Deployment Manager, InTrust Server and InTrust Repository Viewer. If you customize the selection to install individual components, see the requirements for the components you need in the InTrust System Requirements document supplied in the product download. If you use the default selection, the combined requirements are as follows:
Architecture- Operating System
- Microsoft Windows Server 2022
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- CPU
Min. 4 cores (for example, for evaluation purposes).
For any real-world uses, at least 8 cores are recommended.
- Memory
Min. 4GB (for example, for evaluation purposes).
For any real-world uses, at least 8GB are recommended.*
- Additional Software and Services
- Microsoft .NET Framework 4.8 or later with all the latest updates
- Microsoft SQL Server Native Client 11.0.6538.0 or later (version 11.0.6538.0 redistributable package of the client is included in the InTrust distribution) Important: Install the required version of the client in advance, and only then install InTrust.
- In a virtualized environment
If you deploy InTrust on a virtual machine, make sure the CPU and memory requirements above are met, and do not overload the virtual machine host.
- For the configuration database:
- Microsoft SQL Server 2022
- Microsoft SQL Server 2019
- Microsoft SQL Server 2017
- Microsoft SQL Server 2016
- Azure SQL Managed Instance
