IT Security Search
Correlate disparate IT data into an interactive search engine. Seeing
the un-seeable can be a challenge for IT. With billions of events to collect
and review from a variety of sources, both on premises and in the cloud,
it’s difficult to find relevant data and make sense of it. And in the
event of a security breach, either internal or external, the ability to locate
where the breach originated and what was accessed can make a world of
difference.
IT Security Search is a Google-like, IT search engine that enables IT
administrators and security teams to quickly respond to security incidents and
analyze event forensics. The tool’s web-based interface correlates
disparate IT data from many Quest security and compliance solutions into a
single console and makes it easier than ever to:
- Reduce the complexity of searching, analyzing and maintaining critical IT data scattered across information silos
- Speed security investigations and compliance audits with complete real-time visibility
- Troubleshoot widespread issues should an outage or security breach occur
- Configure role-based access, enabling auditors, help desk staff, IT managers and other stakeholders to get exactly the reports they need and nothing more
Features
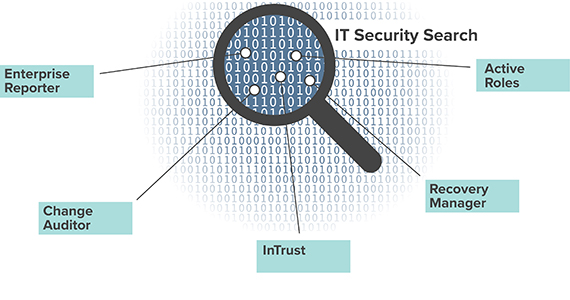
IT Security Search is available as part of several Quest solutions including Enterprise Reporter, Change Auditor, InTrust, Recovery Manager for AD, and Active Roles that pulls data and feeds it into a single pane of glass. From here, you can easily review and act upon all of the various activities in your on-premises or hybrid environment.
State-based data
- Gain critical insights into user, computer and group information, direct and nested group memberships, OU and file/folder permissions, ownership and more across on-premises, Azure and hybrid environments with Enterprise Reporter. Empower IT teams to comprehensively understand their state of security.
- View virtual attributes, dynamic group members, temporal group members and managed units from Active Roles
Real-time security auditing
- Search real-time information about changes to critical objects and sensitive data, whether on premises or in Office 365 and Azure Active Directory (AD), with Change Auditor.
- Supplement native audit details with the actual user who initiated a change to AD, even if it was initiated through Active Roles
Collect and archive logs
Compressed, indexed, online repository
Object recovery
Specifications
- Compatibility
The following versions of data-providing systems are supported in this version of IT Security Search:
- InTrust 11.4.1, 11.4, 11.3.2, 11.3.1, 11.3
- Change Auditor 7.1, 7.0.4, 7.0.3, 7.0.2, 7.0.1, 7.0, 6.9.5, 6.9.4, 6.9.3, 6.9.2, 6.9.1, 6.9
- Enterprise Reporter 3.2.1, 3.2, 3.1, 3.0
- Recovery Manager for Active Directory 10.1, 10.0.1, 10.0, 9.0.1, 9.0, 8.8.1
- Active Roles 7.4.1, 7.4, 7.3.2, 7.3.1, 7.2.1, 7.2, 7.1
- Software Requirements
- Operating system:
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012 R2
- Microsoft Windows Server 2012
- Microsoft Windows Server 2008 R2
- Additional software:
- Microsoft .NET Framework 4.7.2 or later
- Microsoft Windows PowerShell 3.0 or later
- Microsoft SQL Server 2012 or later (all editions). This is a requirement of the IT Security Search Warehouse component, which needs it for internal configuration management.
Additional requirements for the Recovery Manager for Active Directory connector:
- Enable remote commands in Windows PowerShell. For details, see https://technet.microsoft.com/en-us/magazine/ff700227.aspx.
- The PowerShell script execution policy must be set to RemoteSigned. Run the following cmdlet:Set-ExecutionPolicy RemoteSigned
Additional requirements for the Active Roles connector:
- Active Roles Management Tools
- The PowerShell script execution policy must be set to RemoteSigned.
- Operating system:
- Browser Compatibility
The IT Security Search Web interface works correctly with the following browsers:
- Microsoft Edge
- Microsoft Internet Explorer 11 or later
- Google Chrome 72.0 or later
- Mozilla Firefox 65.0 or later
The minimum supported monitor resolution is 1024x768.
- Hardware Requirements
- CPU: 6 cores minimum; 16 cores recommended
- RAM: 8GB minimum; 16GB or more recommended
- Disk: 200GB (SSD recommended); disk space requirements are very dependent on the volume of Enterprise Reporter data being processed, because the index size varies proportionally; the indexes for Change Auditor and InTrust data do not consume any disk space on the IT Security Search computer, because they are located in the data stores used by these systems
- If you deploy on a virtual machine, make sure the CPU and memory requirements above are met, and do not overload the virtual machine host
To find out the disk requirements for IT Security Search installation please refer to the IT Security Search Support Page.
