Einfaches, unkompliziertes, Cloud-basiertes Mobile Device Management
Infelizmente o evento Einfaches, unkompliziertes, Cloud-basiertes Mobile Device Management já expirou.
Você também pode se interessar por.

Melhores maneiras de estender a segurança e o gerenciamento de endpoint para dispositivos móveis
Combine a proteção de endpoint e o Gerenciamento de Dispositivos Móveis (MDM)
Leia o White Paper
Getting Control of Your BYOD Program with UEM
Take a unified approach to endpoint management to reduce complexity and security concerns. Track and manage every mobile endpoint with KACE MDM.
Assista ao webcast
IT Asset Management - Evolving Past the Spreadsheet of Machines
The drive to unified endpoint management (UEM) aims to simplify and unify the deployment, management, and security of all kinds of endpoints, from laptops and printers, to mobile devices, smart devices and the Internet of Things (IoT). However, in order t
Leia o White Paper
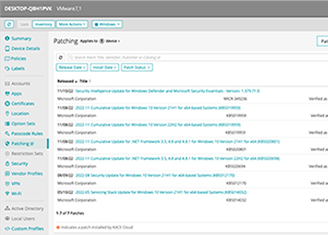
Protect Your Network By Automating Endpoint Security
Stop struggling to manage and protect all the disparate devices connecting to your network. Discover why automated patching is a key component of any unified endpoint management (UEM) security strategy and how KACE solutions can help you safeguard your network and protect it from potential cybersecu
Leia o White Paper
FLASH NEWS: QUEST E ONE IDENTITY
Junte-se a nós para uma emocionante sessão online onde vamos explorar as mais recentes inovações da Quest e One Identity. Nossos especialistas irão destacar as novas
Participar de evento
Está a subestimar os riscos de segurança do seu endpoint?
Está a subestimar os riscos de segurança do seu endpoint? Aprenda os 5 passos para combater o cibercrime no endpoint
Visualizar infográfico