How to reduce AD security risks and insider threats
 01:32
01:32
Hank the Hacker is back and he's ready to attack your Active Directory (AD) environment, whether on-premises or in the cloud. Worse yet, this time he brought friends. With Disgruntled Dan and Careless Craig, he has even more leverage to take control. That's why it's so important to get protected.
Read this informative e-book, Nine Best Practices for AD Security, and discover what you can do to protect your environment from insider threats. Explore:
- Why attackers target AD and how the growing popularity of Office 365 increases the threat
- What an AD security breach means to the organization
- Why it is difficult to secure Active Directory using native auditing alone
- How a typical insider threat unfolds and how to identify common insider threat indicators
- How following nine critical security best practices will help you minimize the risk of the internal threats to the availability, confidentiality and integrity of your AD
Related videos

Recovering from an AD security breach or disaster
Join experts Sean Metcalf and Brian Desmond as they discuss the best practices for quickly dealing with and recovering from AD security breaches.
Duration: 04:15
Prepare for destructive AD cyber-attacks
Learn how you can prepare for – and recover from – a destructive attack on your Active Directory.
Duration: 10:59

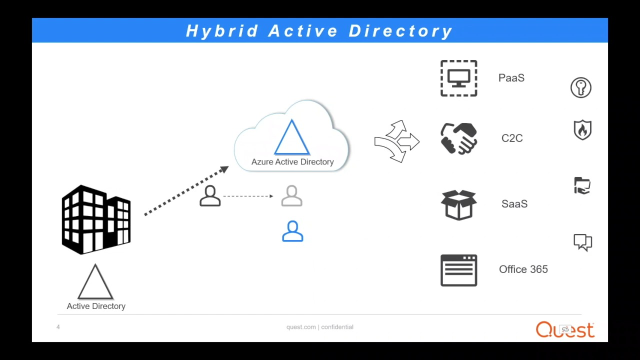
How to Overcome Common Hybrid AD Security Risks
Organizations like yours are sprinting to Microsoft cloud services, such as Office 365 and Azure Active Directory (AD). But as your cloud — and hybrid — footprint expands, so does your security risk. That’s because in a hybrid AD environment, you face all the security limitations of native AD plus those of Azure AD. That means you need to manage double the surface area to overcome potential data breaches and insider threats caused by hackers like the star of the video above — Hank. Hank’s big prize? Your Active Directory environment. It’s his crown jewel, and, if he cracks it, he controls your network, its data, the devices on it — the whole shebang. So, are you ready to do what’s necessary to stop Hank the Hacker and a million others like him?
Duration: 01:22
Current state of AD security
Join Sean Metcalf, Microsoft Certified Master, as he discusses what organizations are seeing and missing when it comes to Active Directory security.
Duration: 03:01

Common AD security pitfalls
Join Sean Metcalf, Microsoft Certified Master, as he discusses the most common mistakes organizations make when it comes to Active Directory security.
Duration: 03:21
Is your AD environment safe from the dark side?
See how Quest Software and One Identity can protect your organization from Hank the Hacker and other forces poised to steal AD-controlled credentials and your valuable data.
Duration: 03:10