Hi. I'm Shawn Barker. I'm Product Manager. And today I'm going to demonstrate how Change Auditor can audit user logon activity.
Change Auditor allows you to track, alert, audit, and report on user activity from logon to logoff. And this is important whether you need to satisfy external compliance regulations, internal compliance needs, or your security teams. In either case, the complete tracking of user activity is critical.
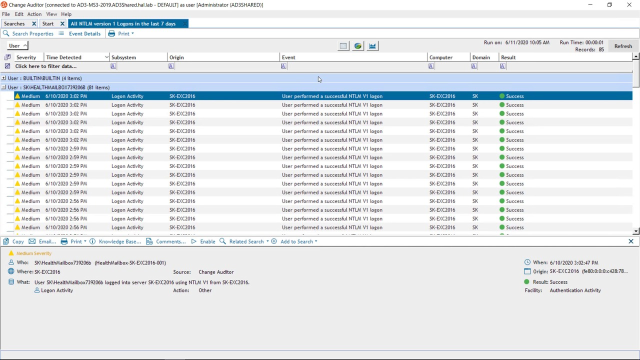
So I'm going to start from the Overview screen here. I'm looking at all the logon activity. But I can very quickly group this by logon type, so I can easily discern user logons by the different types, whether it's interactive, remote, local, or network. And then I can quickly drill down into an area of concern.
So, for example, failed interactive logons. I'll take a look at a recent logon failure here. And Change Auditor presents every event, all the important information, in a simple, readable format. So I can see the user that failed to log on-- [? Lance ?] [? Strewn-- ?] the computer that they attempted to log onto, but also the workstation or server where they logged on from, including the IP address.
But what's really powerful about Change Auditor is from this result I can very quickly generate a view of all the related user activity. So if I want to take a look at everything else this user's been up to recently, I can see the failed logons here, but also more recently everything else that this user's been involved in. For example, they were added to a local admins group on the SQL Server.
So if I go back to the Overview screen here, the other thing that Change Auditor for Logon Activity does is correlate all the events that are related to a user's logon session. So that includes the logon, it includes when the computer is locked, or when the screensaver's activated, but also the logoff, whether it happened because the user logged off, or the computer was shut down. And it correlates all of these into one single event that gives an overview of the user's session.
So if I click on an event, I can see the entire view of a user's session. And then this includes when they logged on, how long they we're logged on for, including all those events I just mentioned. So I can see the entire picture of the user's logon sessions.
That was a standard Change Auditor client. I'm also going to log into the Change Auditor Web Client. So all this information is also available from the web, so that as an administrator, I can log in and get access to this from anywhere.
So let me take one of the built-in searches here. Say all logon activity in the last-- all failed logons in the last month. So I can run this search, and then from the results, I can actually use the timeline feature of Change Auditor to basically plot all these events onto an interactive timeline where I can very quickly inspect important events.
So, for example, the events that just occurred on the SQL Server, I'll see these highlighted on my timeline here, and I can drill into those and see the related activity. And then from here, I can click on an individual event, and it'll take me to all the event details that I saw earlier.
So the other thing I want to be able to do is schedule alerts and reports. So there's certain types of behavior that I want to see on a regular basis; I want to be notified proactively. So great thing about Change Auditor is that I've got a number of built-in reports or searches here. And any search can be modified and then turned into an alert or a report.
So, for example, a couple of simple cases here. I might want to be alerted, not to all failed logons, but failed logons for people in the domain admins group, so when privileged users attempt to log on and fail, or I might want to see successful logons by, or interactive logons by, service accounts, for example. So I can take any search here, and then customize it and save a copy.
So in this case, I want to-- let's go with the domain admins. So all failed logons by domain admins. The search is defined by the five W's here, so the who, what, when, where. In this case, I want to get more specific, so I want to narrow down the search by who. So in this case, I will go with the domain admins group. And now, this way, I'm only going to see fails from the domain admins group.
I can also get more specific about what types of failures. In this case, I have all the logon failures defined here, which servers they failed to log onto, but let's just leave it as the domain admins group. And then from this search, I can either schedule a report-- so, for example, your auditors group may want to see a regular report of all privileged access, so any time anybody logs on with a privileged account. And you could schedule that report to be sent once a week, for example, or I can set up an alert.
So let me do this for failed logons by domain admins. And I'll configure it to be sent to me as an alert, and then save this search. And now, any time somebody from the domain admins fails to log in, I'll receive an alert in my inbox. And it gives me all the information that I see in the console in terms of who attempted to log in, where, and the reason for the failure.
 05:02
05:02
