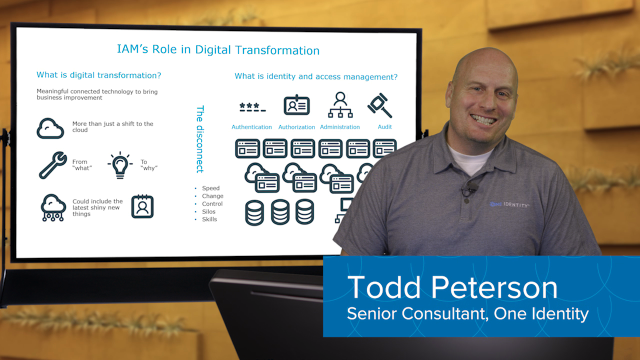
[MUSIC PLAYING] Hi. My name is Todd Peterson. I'm on the team here at One Identity. And today, we're going to talk about digital transformations, and specifically what identity and access management's role is in a digital transformation. So let's turn to the board here.
First off, let's go with some definitions. What is a digital transformation? It means a lot of things to a lot of different people, but basically, what I consider it as is implementing meaningful connected technology to bring about business improvement.
So OK, that sounds great. What does it really mean? It's more than just a shift to the cloud. Although moving to the cloud is often a big part of a digital transformation, simply because you move some stuff to the cloud doesn't mean you have done a digital transformation. It's kind of the shift in thinking from what you need to do to why you need to do it. What's your objectives? What's your business mission?
Why are you trying to do these things? If it's just to implement some new technology, that's not cool. If it's to further your business, to serve your constituents, to make money to do whatever you're in business to do, that's what a digital transformation is meant to do. And often, it will involve some of these new and shiny things that you hear so much about-- internet of things, mobile access, IOT. All that type of stuff is all part of a digital transformation.
So now, let's switch over to the other side. What is identity and access management? At its core, Identity and Access Management, or IAM, is about giving people access to the stuff they need to do their jobs. So there's four main parts of that. The first is authentication. How do you get people to log on? How do they get access to things?
Once they're accessed, you have to worry about authorization. What do they do? What are they allowed to do? What are they not allowed to do? Once they have been authenticated, what are they authorized to do?
And then administration-- how do you set up that authentication and authorization to make sure that it's done correctly? How do you make it efficient? How do you put the right people in charge? And then finally, audit-- how do you make sure that all those things happen in a way that follows the rules, that you can be compliant, that you're more secure and all that?
So that's cool. The problem is you have to do it for everything you've got. You've got all your on-prem stuff that you've always had. You have to do authentication, authorization, administration, audit for that stuff. And then in the digital transformation, you have this new cloud stuff that's coming into play. You have to do the same things for that.
So digital transformation is all about enabling and empowering and doing stuff better, whereas identity and access measurement is all about doing stuff securely and doing it right. So there's kind of a disconnect there. Problems are that normally, identity and access management can't move at the speed of digital transformation.
Older IAM technologies are kind of stuck in their ways, and they're not nimble enough to take the pace of a digital transformation. There's lots of change. With digital transformation, you've got things happening very fast, happening all the time, and you constantly have to do authentication, authorization, et cetera for all of those things. That's hard to do with old types of technologies.
Control with a digital transformation-- a lot of the things that you normally could control in an on-prem environment are moving out of your control. They're now out in the cloud. Somebody else has got control of them. So you're losing some of that control, and that results in a lot of silos.
So you have-- authentication happens one way for this application, another way for that application. This cloud application does it the third way. So you're having a lot of disconnect there. And then skills-- the skills that your staff currently has may not match the skills they're going to need for a digital transformation.
So let's talk about how you can do digital transformation right with identity and access management. First off, you've still got all those things happening. You have authentication. You have authorization. You have administration, and you have audit. And you want to do those things in a unified manner for all of your new cloud resources as well as for all of the on-prem resources that you've always had.
So some of the things that you need to do for authentication is single sign-on. You want to provide people a single way to get to everything they need, whether that's in the cloud or whether that's on-prem. Remote users-- often, you find that you have to give remote uses a different, more difficult way to access things. You don't want that. You want them to access things as easily and as seamlessly as possible.
And then sometimes you want to secure their access better. So you want to use multi-factor authentication. All of those things come into play with the authentication capabilities in a digital transformation.
Now let's move over to authorization. You want to define what people do once. You want a single role, a single idea of what it means to be a particular user to apply to everything, your cloud resources as well as your on-prem resources. You want provisioning or the setting up, the administration of those things, to happen in a single action that covers everything, whether it's in the cloud, whether it's not in the cloud.
You want attestations or those compliance activities that you have to do to prove that those things are happening in the right way-- to happen once for everything as opposed to once for this application, a different way for that application, a third way for this database or whatever.
 08:10
08:10
