KACE Desktop Authority
Centralized, secure desktop management software for Windows environments. With KACE® Desktop Authority you can proactively configure, manage, secure and support each unique user workspace, quickly and easily, through a single console. Minimize the hassles of deploying and securing individual devices by customizing devices at the first log-in while configuring the firewall and controlling browser security for physical, virtual and published Windows environments.
Secure, privileged access to systems and data
Business stakeholders require greater flexibility in IT operations, but administrators must still maintain a secure and consistent user environment. They can no longer rely on the traditional model of managing only the machine. Each user needs to be granted the right access to the right resources regardless of the device used.
KACE Desktop Authority is the foundation for our centralized, secure desktop management software for Windows environments, KACE Desktop Authority Management Suite. Along with KACE Privilege Manager, you can maintain the balance between security and user productivity while saving IT resources.
Benefits
Customize Devices
Manage Applications
Maintain Identities
Empower Users
Features
Real-time targeting engine
User environment configuration
Windows environment management
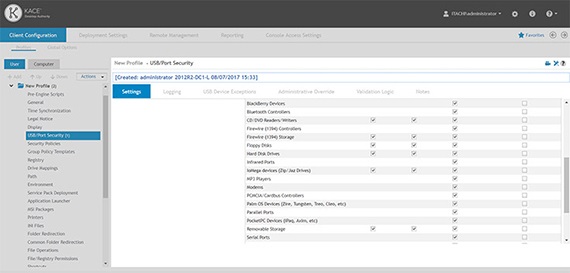
Device security
Remote user support
Specifications
- Operating systems
- Windows Server 2019
- Windows Server 2008 R2 Standard/Enterprise
- Windows Server 2012 R2 Standard/Enterprise
- Windows Server 2008 Standard/Enterprise (32/64 bit)
- Windows Server 2012
- Windows Server 2016
- Domain controllers
- Windows Server 2008 domain
- Windows Server 2012 domain
- Windows Server 2016 domain
- Windows Server 2008 R2 domain
- Windows Server 2012 R2 domain
- Database server
- Microsoft SQL Server version 2008 or higher
- Installed if necessary
- Microsoft .NET Framework version 3.5 SP1
- Microsoft Visual C++ 2005 Redistributable Package
- Microsoft Internet Information Services (IIS) 7 or higher
- Microsoft .NET Framework, Hotfix KB981119
- Microsoft SQL Server 2008/2014 R2 Express — Installed if an existing SQL Server instance is not selected
- Browsers supported (Console)
- Internet Explorer® 11
- Chrome™ 44 or higher
- Firefox® 3.8 or higher
- Microsoft Edge™ 25 or higher
- Screen resolution
- 1024x768
- Operating systems
- Windows 7
- Windows 10
- Windows Server 2008 R2
- Windows Server 2012 R2
- Windows Server 2019
- Windows 8.1
- Windows Server 2008
- Windows Server 2012
- Windows Server 2016
- Installed if necessary
- Microsoft Windows Installer 3.1
- Microsoft .NET 2.0 SP1
- Browsers supported
- Internet Explorer® 11
- Chrome™ 44 or higher
- Firefox® 3.8 or higher
- Microsoft Edge™ 25 or later
- Screen resolution
- 1024x768
- One admin-level account with read/write access to all NETLOGON share(s) and to be a member of the local Administrators group on all applicable workstations
- One domain user-level account
