Organizations face consequences for not having a pro-active auditing and compliance solution in place. Consequences such as security breaches, failed IT audits, and system downtime are commonplace. Now despite these consequences, there are many common mistakes that organizations make in regards to their audit and compliance procedures. Some of these mistakes include lack of visibility into who has access to what in the Windows environment. Underestimating user and organizational impact on the environment and failure to plan and manage external and internal audits. Now these mistakes are understandable given the technical challenges that most organizations face.
Some of these challenges include lack of process automation, which does not let the IT department focus on core business priorities. And information that is out-of-date can be inaccurate and result in non-compliance to regulations. Also, manually checking for changes in rights could result in miss-changes, which could spell a security violation. Now to mitigate some of these mistakes, organizations sometimes rely on scripts. However, scripts do fall short in many areas. And that's why there are enterprise reporting solutions available. A good enterprise solution provides better performance for report compilation, better scalability of data collection, built-in report expertise, delegated access to reports, report customizability, and better change review.
And that's where Dell Enterprise Reporter comes in. It provides over 174 out-of-the-box reports that provide an automated scalable solution for auditing, analyzing, and reporting on the Microsoft Active Directory environment, Windows servers, SQL servers, and file servers across the enterprise. Pre-defined and customizable reports make it easy to perform compliance and security assessments, better pre and post-migration analysis, and better file storage capacity planning and monitoring. Today's session is going to focus on Enterprise Reporter for Windows servers.
Some of the features that this module provides, include better access assessment, allowing you to quickly find out in real time where selected users and groups have permissions. Better local policy assessment, to make sure that local security configuration is aligned with domain wide policies. And better permissions reporting, to allow you to collect and report on permissions of shares, files and folders, printers, registry keys, and services in the environment.
Some of the questions that these features allow you to answer are questions like, where does this user group have access to critical unstructured data? Who has administrative access to Windows servers and workstations? How are servers configured, including general computer information, network settings, services running, installed programs, and customer registry keys? And how does the configuration of these servers change over time?
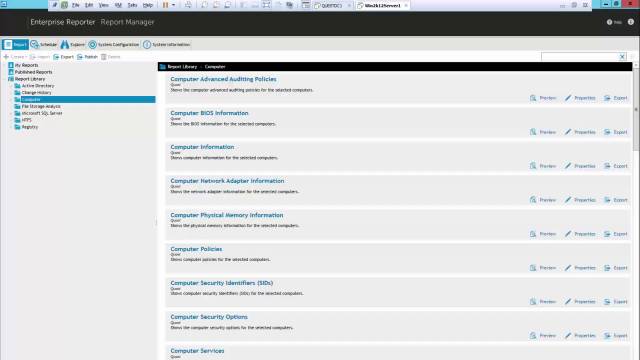
Let's have a quick look at some of the reports that are available out-of-the-box for Enterprise Reporter for Windows servers. First, let's dive into the change history category and the computer change history report. This report is going to show the changes made over time to selected computers. Next, we select the computers that we're interested in reporting against. We hit Run Report. And this is going to show it changes to those computers over time, what properties were modified and what the new value is.
Next, let's delve into the computer category. Let's have a look at the computer information report. This report is going to show computer information for selected computers. Now we're currently looking at all the out-of-the-box reports that are available. The out-of-the-box reports, as well as any custom reports you may create, can be run on an ad-hoc basis like we're doing here. The report output can be saved. It can be exported to a variety of common formats. It could be emailed out to key stakeholders in the environment. We could also take these reports and publish them out to a website to allow users to run those reports on an ad-hoc basis, an as needed basis.
Next, let's have a look at Hot Fix information. In today's climate of daily cyber security attacks, it's important to stay on top of the hot fixes and ensure that these hot fixes are being applied on a regular basis to the environment. This particular report will give you the ability to easily report on the values and determine and visualize which hot fixes have been applied in the environment. Additionally, here we can see all services that are not running as the system account. Not only the services, but other attributes of those services, including name, start up type, the current state of those services, and what the log-on value is.
Next let's go down and have a look at some of the NTFS based reporting. Here let's go in, we'll look at files last accessed and last end days grouped by parent path. Again, flexible filtering is available here with this report. We can specify the time period. We can further specify in filter, based on folders and filed extensions. We'll just accept the defaults here. Run the report. This particular report can be beneficial if you're looking to do any kind of NTFS file cleanup on the servers in your environment. Many reports here in regards to files, folders, permissions, file and folder summary, as well NTFS object attributes. And lastly, here we have a category of reports to allow you to visualize information taken from the registry of the servers in your environment.
Now all of these reports are particularly beneficial as previously stated to establish those security baselines to help you to do more effective and efficient inventory of what's out there in your environment. A common challenge in the Microsoft space is that when you're looking to investigate who has access to what in the environment, it's challenging. Because when someone is granted access to a resource, that access is actually stamped on the resource itself. In other words, there's no central place or directory in which you can go to look and investigate to see what files or folders and unstructured data that John Doe has access to in the environment, in the event of a security breach or a detection of a rogue user.
An Enterprise Reporter for Windows servers allows
 10:03
10:03
