Enterprise Reporter for Windows Servers
Windows Server and OneDrive for Business discovery and reporting across the enterprise. Enterprise Reporter for Windows Servers provides deep visibility into the security and configuration of Microsoft Windows Server, Azure, NAS devices and OneDrive for Business. Armed with this information, organizations can perform security assessments to understand who can access what data, how they got that access, as well as whether it can be shared with others inside or outside the organization. Perform pre-and post-migration analyses and optimize resource and license allocation. As a result, you’ll be empowered to perform more informed strategic planning and proactive management of the IT infrastructure.
Extend your visibility beyond file servers, Azure and OneDrive for Business to other on-premises and Office 365 environments with Enterprise Reporter Suite.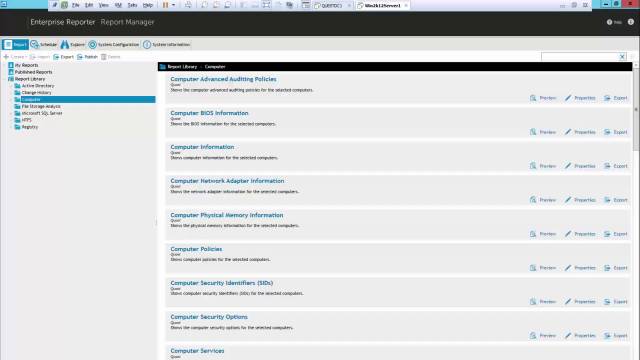 10:03
10:03
Features
Hybrid environment reporting on on-premises and cloud-based permissions
Gain insights into permissions for on-premises and cloud-based resources with easy-to-use reports on who can access:
- On-premises shares, files, folders, printers, registry keys and services
- Cloud-based content posted to OneDrive for Business, including file and folder permissions and whether the content can be shared internally or externally
Compliance and security visibility
Gain visibility into the configuration of critical IT assets in Windows file
servers, NAS devices and OneDrive for Business to comply with security best
practices, internal policies and external regulations. Report on permissions
and access to:
- Files, folders, and shares across your Windows file servers
- Shared files and folders across OneDrive for Business
- Azure resources, including VMs, disks, network security groups, storage accounts and more
Improved insights with IT Security Search
Access assessment
Pre- and post- migration assessment
Hosted resource optimization
Local policy assessment
Scalable data collection
Efficient storage
Customizable reports
Automated reporting workflows
Specifications
- Memory
- Minimum: 16 GB RAM
- Recommended: 16 GB RAM
- Processor
- Intel or AMD 2 GHz multiprocessor (with at least 2 cores)
- 64-bit processor
- Hard disk space
Disk space requirements will vary with the Enterprise Reporter components you install:
- Server—10 GB
- Configuration Manager—2 GB
- Discovery Node—10 GB for installed files, plus extra space (10GB-100GB) for processing discoveries. Space required varies with the amount of data collected.
- Report Manager—10 GB
- Database size varies with the amount of data you collect
- The file share that you use for the Shared Data Location will require space for storage of collected data. Space required varies with the amount of data collected.
- Total disk size if all components are on the same system—100 GB
- Memory
- Minimum: 16 GB RAM
- Recommended: 16 GB RAM
- Processor
- Intel or AMD 2 GHz multiprocessor (with at least 4 cores)
- 64-bit processor
- Hard disk space
100 GB or more for larger environments
The Enterprise Reporter database is the storage location of all data collected for reporting. As such, the amount of hard disk space required is directly related to the amount of data being collected. The Database Size Estimator tool shipped with Enterprise Reporter can help determine how much space will be required.
SQL Server performance is needed to support inserting data into the database tables and to support querying that data for reporting purposes. To improve the performance of data collection or reporting, consider enhancing the SQL Server memory and processor.
Larger environments may have additional requirements for memory, processor, and hard disk space. There are many factors that can effect these requirements. For additional information please see release notes.
The following operating systems are supported for Enterprise Reporter components.
NOTE: It is not recommended that the server or console be installed on a domain controller.
- Computers
- Windows Server® 2016
- Windows Server® 2012 R2
- Windows Server® 2012
- Windows Server® Core 2012 R2
- Windows Server® Core 2012 R2 Cluster
- Windows Server® Core 2012
- Windows Server® Core 2012 Cluster
- Windows Server® 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1 (64 bit) Cluster
- Windows Server® 2008 with Service Pack 2 (64 bit)
- Computers
- Windows Server® 2016
- Windows Server® 2012 R2
- Windows Server® 2012
- Windows Server® 2008 R2 with Service Pack 1
- Windows Server® 2008 with Service Pack 2 (64 bit)
- Windows® 10
- Windows® 8.1
- Windows® 8 (64 bit)
- Windows® 7 with Service Pack 1 (64 bit)
- Windows Vista® with Service Pack 2 (64 bit)
- Computers
- Windows Server® 2016
- Windows Server® 2012 R2
- Windows Server® 2012
- Windows Server® Core 2012 R2
- Windows Server® Core 2012 R2 Cluster
- Windows Server® Core 2012
- Windows Server® Core 2012 Cluster
- Windows Server® 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1 (64 bit) Cluster
- Windows Server® 2008 with Service Pack 2 (64 bit)
- Domain Functional Levels
- Windows Server® 2016 Functional Level
- Windows Server® 2012 R2 Functional Level
- Windows Server® 2012 Functional Level
- Windows Server® 2008 R2 Functional Level
- Windows Server® 2008 Functional Level
- Windows Server® 2003 R2 Functional Level
- Computers
- Windows Server® 2016
- Windows Server® 2012 R2
- Windows Server® 2012
- Windows Server® Core 2012
- Windows Server® 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1
- Windows Server® 2008 with Service Pack 2 (64 bit and 32 bit)
- Windows Server® 2003 R2 with Service Pack 2 (64 bit)
- Windows Server® 2003 R2 with Service Pack 2 (64 bit and 32bit)
- Windows® 10
- Windows® 8.1
- Windows® 8 (64 bit and 32bit)
- Windows® 7 with Service Pack 1 (64 bit and 32 bit)
- Windows Vista® with Service Pack 2 (64 bit and 32 bit)
- Windows® XP Professional with Service Pack 3 (64 bit and 32 bit)
- Network Attached Storage (NAS) Devices
- Dell FluidFS 6.0
- Dell FluidFS 5.0
- NetApp® Filer - Data ONTAP® 8..x – 9.x and above (Cluster mode is supported as of version 8.2)
- EMC Isilon OneFS (Collections require a secure connection to Isilon with a valid certificate)
- EMC VNX 7.1.47.5 X (Supported by collecting as a Windows Server)
- EMC VNX 7.0.35.3 X (Supported by collecting as a Windows Server)
- Computers
- Windows Server® 2016
- Windows Server® 2012 R2
- Windows Server® 2012
- Windows Server® Core 2012
- Windows Server® 2008 R2 with Service Pack 1
- Windows Server® Core 2008 R2 with Service Pack 1
- Windows Server® 2008 with Service Pack 2 (64 bit and 32 bit)
- Windows Server® 2003 R2 with Service Pack 2 (64 bit)
- Windows Server® 2003 R2 with Service Pack 2 (64 bit and 32bit)
- Windows® 10
- Windows® 8.1
- Windows® 8 (64 bit and 32bit)
- Windows® 7 with Service Pack 1 (64 bit and 32 bit)
- Windows Vista® with Service Pack 2 (64 bit and 32 bit)
- Windows® XP Professional with Service Pack 3 (64 bit and 32 bit)
- Network Attached Storage (NAS) Devices
- Dell FluidFS 6.0
- Dell FluidFS 5.0
- NetApp® Filer - Data ONTAP® 8..x – 9.x and above (Cluster mode is supported as of version 8.2)
- EMC Isilon OneFS (Collections require a secure connection to Isilon with a valid certificate)
- EMC VNX 7.1.47.5 X (Supported by collecting as a Windows Server)
- EMC VNX 7.0.35.3 X (Supported by collecting as a Windows Server)
- SQL Server Instances
- SQL Server® 2017
- SQL Server® Clusters
- SQL Server® 2016
- SQL Server® 2014
- SQL Server® 2012
- SQL Server® 2008 R2
- SQL Server® 2008 with Service Pack 2
- SQL Server® 2005 with Express Service Pack 3
- SQL Server® 2005 with Service Pack 3
- Exchange Servers
- Exchange Online™
- Exchange® 2016
- Exchange® 2013
- Exchange® 2010
- Exchange® 2007
- Exchange® Mixed Modes (2007-2010, 2010-2013, 2007-2013)
The follow versions of Active Roles are supported as targets of Active Directory discoveries. See the Active Roles web site for hardware and software requirements for your version of Active Roles:
- Active Roles 7.2.1
- Active Roles 7.1.2
- Active Roles 7.0.4
- Active Roles 7.0.2
- Active Roles 6.9.0
Enterprise Reporter can be configured to send discovery information to the following versions of IT Security Search. See the IT Security Search web site for the hardware and software requirements for your version of IT Security Search.
- IT Security Search 11.4
- IT Security Search 11.3
The following versions of SQL Server® are supported for the Enterprise Reporter database. See the Microsoft® web site for the hardware and software requirements for your version of SQL Server®:
- SQL Server® 2017
- SQL Server® 2016
- SQL Server® 2014
- SQL Server® 2012
- SQL Server® 2008 R2
- SQL Server® 2008 with Service Pack 2
- SQL clusters and database mirroring are supported for your
deployment, including
- SQL Server® 2016 Always On
- SQL Server® 2014 Always On
- SQL Server® 2012 Always On
- Using SQL Server Certificates
SSL Encryption of SQL Server Connections using Certificates
Enterprise Reporter can be configured to work with a SQL Server® instance. To secure communications while working with Enterprise Reporter, data sent over connections to the SQL Server can be encrypted using an SSL certificate.
The steps required to configure this encryption are as follows.
- Using the Microsoft Management Console (MMC):
- install the Certificates snap-in for the SQL Server® host computer
- import the certificate to the SQL Server® host computer
- Using SQL Server Configuration manager:
- configure the SQL Server® to use the certificate
- configure the SQL Server® to force encryption
- Restart the SQL Server® host computer
- Import the certificate to all Enterprise Reporter computers that
will need to communicate with the SQL Server®, such as:
- Enterprise Reporter server host computer
- Enterprise Reporter nodes
- Enterprise Reporter Configuration Manager host computer
- Enterprise Reporter Report Manager host computer
- Install Enterprise Reporter on a host computer
- Using the Microsoft Management Console (MMC):
The following required software is required for Enterprise Reporter.
- Microsoft®.NET Framework 4.6
- Microsoft®.NET Framework 4.0 (Full)
- Microsoft®.NET Framework 3.5 Service Pack 1
- Microsoft® Excel® (required to view reports exported as spreadsheets)
- Microsoft® Excel® 2010
- Microsoft® Excel® 2013
- PowerShell™ 3.0
- Active Roles Required Software
To collect Active Roles information, the following software is required on the computer where the Enterprise Reporter Configuration Manager is installed and on the computer where the Enterprise Reporter node is installed:
- ADSI Provider (the version must match the Active Roles version)
For more information and installation instructions, see the Active Roles Quick Start Guide. The following additional considerations are required:
- There must be a trust between the Enterprise Reporter domain and the Active Roles domain.
- The credentials used for the Active Roles discovery must have access to the Active Roles domain.
- Exchange Required Software
To collect Exchange® 2007 information, the following additional considerations are required:
- Exchange® 2007 Management Tools must be installed on the computer where the Enterprise Reporter node is installed and must be in the same forest as the 2007 Exchange Organization.
- It is highly recommended to put the computer where the Enterprise Reporter node is installed within the target Exchange® 2007 domain.
To collect Exchange mailbox folders, the following additional considerations are required:
- Impersonation needs to be configured on the Exchange
organization. Refer to your Exchange Server document or use the
following method to set up role assignments.
- Powershell can be used to add an assignment
New- ManagementRoleAssignment–
Name: impersonationAssignmentAdministrator-
Role: ApplicationImpersonation –User:Administrator
- Alternatively, you can create an administrator role with ApplicationImpersonation role assigned to it and add the required account as a member (or assign ApplicationImpersonation role to an existing administrator role)
- Powershell can be used to add an assignment
- Impersonation needs to be configured on the Exchange
organization. Refer to your Exchange Server document or use the
following method to set up role assignments.
- OneDrive Required Software
To collect OneDrive information, the following additional software is required:
- Microsoft SharePoint Online Management Shell
NOTE: PowerShell 3.0 and Microsoft SharePoint Online Management Shell are required on the node machines to collect OneDrive configuration settings.
NOTE: In addition, for OneDrive configuration settings to be collected successfully, an authorized connection must be established to the SharePoint Online service. To allow for credentials to be specified for your tenant, the “LegacyAuthProtocols” setting must be enabled on your tenant. To set this on your tenant, run the following commands using the Microsoft SharePoint Online Management Shell. This action must be performed on any node machine with Microsoft SharePoint Online Management Shell installed.
Set-ExecutionPolicy -Scope Process -ExecutionPolicy RemoteSigned
Import-Module -Name Microsoft.Online.SharePoint.PowerShell
Connect-SPOService -Url "<full tenant name>"
Set-SPOTenant -LegacyAuthProtocolsEnable $True
Disconnect-SPOService
- Azure Required Software
To collect Azure information, the following additional software is required:
- Microsoft Azure Active Directory Module for Windows PowerShell
NOTE: Microsoft Azure Active Directory Module for Windows PowerShell is required on the node machines to collect multi-factor authentication attributes for Azure Users.
The following services are required on the Enterprise Reporter server and nodes.
- Net.TCP Port Sharing
The following services must be enabled on discovery targets for collections.
- Remote Registry
- Windows Management Instrumentation (WMI)
For more information see the release notes.
