Since starting my tenure at Quest, I have had multiple customers ask me “how can I use Change Auditor to audit DNS changes in my environment?” At first thought, this seems like an easy task to complete. Change Auditor comes with many DNS related events to accomplish the goal. Unfortunately, upon diving deeper, it becomes abundantly clear that the difficulties begin once the user enables these events to audit. The goal of this post is to educate customers on not only Change Auditor’s ability to audit DNS, but to offer insights about how to harness the solution’s power in their environments.
Change Auditor DNS Events
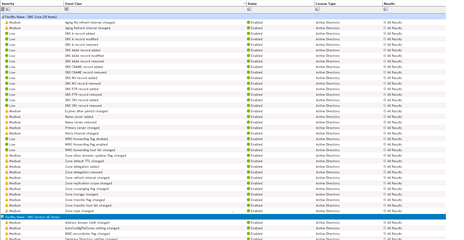
Out of the box, Change Auditor includes an abundance of DNS related events for auditing. Based on the nature of the events, some are prone to generating a lot of “noise” within your environment. It creates what I call a “Boy that Cried Wolf Syndrome.” Meaning that they generate so many events that users invariably ignore or disable them all in an effort to control event sprawl. While disabling events does limit them in number, it also eliminates users’ ability to audit anything DNS related.
Figure 1: Change Auditor includes a multitude of DNS Events ready to audit upon installation.
Tip 1 – Disable Only Unwanted Events
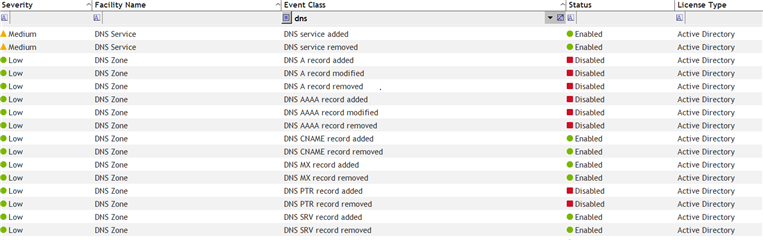
Change Auditor comes with the ability to disable (or enable) any event that the system audits. This is intended to allow our customers to audit only what they need to. Utilizing this feature is step one in the process of eliminating unnecessary DNS events in your environment. Simply turn on the DNS related events, and wait and see what events come in. You can then use this information to disable any of the events that are unnecessary to your audit requirements. Once disabled, you will no longer see any events generated for that activity.
Figure 2: Change Auditor allows any event to be disabled allowing customers to audit only what they need in their environment.
Tip 2 – Audit PEOPLE Making DNS Changes
When Dynamic DNS is involved with DHCP, a TON of Change Auditor events can be created. Our experience tells us that customers often have 60% or more (one was actually 90%) of their Change Auditor database filled with DNS related events. Moreover, we have found that the vast majority of these events are ignored as so many are system (non-human activity) related. When drilling down into this problem it becomes clear that Dynamic DNS events are inconsequential to our customers. What they care about is PEOPLE modifying DNS records and deciphering who they are.
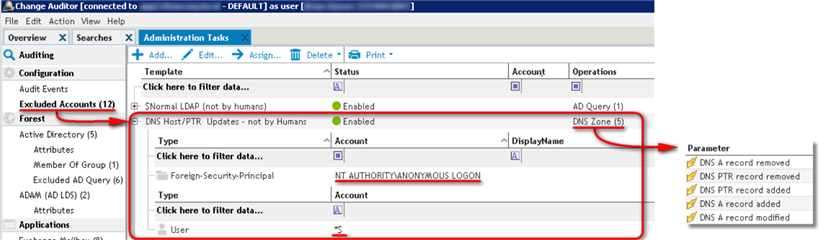
Change Auditor features “Excluded Accounts” functionality built in. This feature is designed to perform exactly as its nomenclature would indicate. It allows Change Auditor administrators to add accounts (or groups) to the “Excluded Accounts” list. Once added, activity initiated by these users (or members of the group added) will not generate Change Auditor events. By adding NT AUTHORITY\ANONYMOUS LOGON and *$ (computer accounts end in “$”) to the excluded accounts list, you will be eliminating the events generated by non-human activity. This feature also includes an operations list where one can associate specific events to these accounts ensuring that only those specified events will be ignored. All other activity generated by that account will continue to be audited.
Figure 3: Change Auditor comes with the “Excluded Accounts” feature in order to add accounts whose activity should not be audited.
Tip 3 – Create DNS Purge Jobs
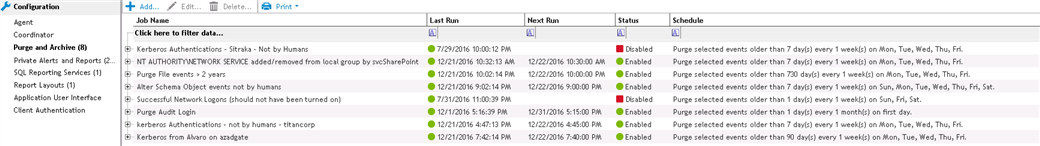
Anytime additional auditing is activated within Change Auditor, the rate at which its database grows will increase. This especially holds true with DNS auditing. A recommendation we always give customers going down this route is to set up specific purge jobs to clear DNS events more frequently than other events. For example, set up a purge job that clears DNS related events older than 30 days old so your database avoids unnecessary expansion. Keep in mind, this threshold is specific to your organization’s auditing requirements.
Figure 3: Create purge jobs to clear out DNS events more frequently in order to keep database size down.
Auditing DNS related events can be a tricky task to complete. Many customers have attempted, but have ultimately acquiesced to the overwhelming amount events created once enabled. By following the recommendations above, Change Auditor will give a view into the DNS related events required, without compromising the significance of its events or the performance of the auditing solution.
The Author would like to recognize Brian Hymer and Robert Tovar for their contributions to this content.