“We’re…looking for big, juicy, egregious cases,” said HIPAA compliance chief enforcer, Roger Severino, Director for the Office of Civil Rights. In part eight of my blog series 10 predictions for 2019: What's in store for Windows and Office 365 pros, we will dive into the rise in HIPAA violations to understand what is technically required to safeguard protected health information. We’ll also explore why organizations are failing this part and what they should look for in HIPAA compliance software in 2019.
Safeguard protected health information: we mean it this time!
Since 2016, seven figure penalties have become the norm rather than the exception because of careless and “egregious” handling of PHI.
Prior to 2016, the Department of Health and Human Services (HHS) as well as state attorneys general would slap you on the wrist, with little to no fines, for violations. But, something funny happened; cybercriminals found that they could derive more value from stolen PHI than your credit card.
This isn’t a statement on the size of your credit limit. It’s about the endless financial possibilities related to identity theft, medical fraud, financial misdemeanors, tax fraud and insurance fraud. Black-market PHI data goes for upwards of $1,000 (way more than those Marriott reward points)!
This is why Severino says there will be “no slowdown in our enforcement efforts” of HIPAA compliance.
As of early December 2018, there are 226 incidents under investigation for unauthorized access/disclosure and hacking/IT incidents, as well as an additional 50 already resolved from 2018 for the same types of breaches.
They’ve given organizations plenty of time to get this right and prove that they are safeguarding PHI continuously.
The technical safeguards to reduce unauthorized access to PHI
The HIPAA Privacy Rule establishes standards for protecting PHI, including who should have access to it. The Security Rule operationalizes these standards by addressing technical, physical and administrative safeguards for the protection and transmission of electronic PHI (ePHI).
What we’re concerned with today, and probably why you as a Windows or Office 365 professional are reading this, is the technical safeguards section (§ 164.312) of the Security Rule. To meet HIPAA requirements for protecting ePHI, organizations need to address the following:
- Access controls — Allow only authorized persons to access e-PHI (45 C.F.R. § 164.312(a)).
- Audit controls — Record and examine access and other activity in information systems that contain or use e-PHI (45 C.F.R. § 164.312(b)).
- Integrity controls — Ensure that e-PHI is not improperly altered or destroyed and have electronic measures to confirm it (45 C.F.R. § 164.312(c)).
- Authentication controls — Make sure the person accessing e-PHI is who they say they are (45 C.F.R. § 164.312(d)).
- Transmission security — Protect e-PHI in transit against unauthorized access (45 C.F.R. § 164.312(e)).
The HIPAA compliance technical safeguards are more than an assessment
On a regular basis, HIPAA-compliant organizations must prove they are reasonably and appropriately meeting these technical safeguards (emphasis added to highlight the lovely vagueness provided by HHS to which covered entities are held).
Organizations do this through a security assessment.
Looking back on the 276 HIPAA violations under investigation in 2018 related to failures in providing technical safeguards for PHI, it’s safe to assume that many of those organizations did pass an assessment at one time. They probably even have a written policy about this. But, proving HIPAA technical safeguards are in place is more than an assessment of a point in time.
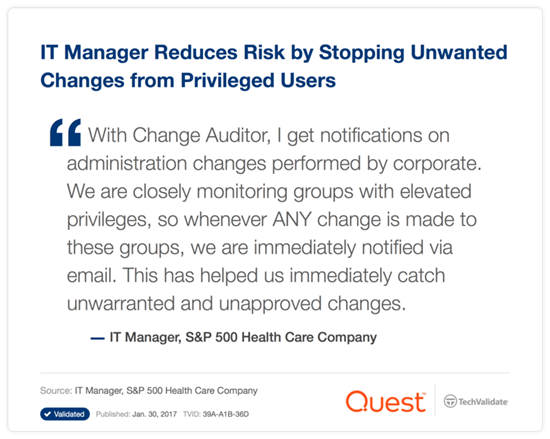
Anyone can pass one of these assessments if they have the processes in place, but the rest of the audit is showing you are following those processes continuously. This is where we are seeing organizations trip up and why the fines have been increasing since 2016.
What used to pass for a HIPAA audit and why it’s not working anymore
Prior to strict enforcement, HIPAA compliance could be proved by spitting out a modifiable CVS report that showed the current state of a compliance-affecting item. Then there would be ad hoc communications around the report with the auditor, such as, “Explain your Domain Admins group and why these folks are in it.”
There was no requirement or enforcement to show when, how and by who the members were added. The auditors would just have to take their word for it and trust that no one manipulated the report to hide discrepancies.
This was less than optimal, but it worked. And, by “worked,” I mean a healthcare organization would fail the integrity part of the audit, and simply get a warning to fix it by the next audit. No one really needed to solve the problem — and no one did.
“Less-than-optimal” doesn’t work anymore for HIPAA compliance. Organizations need to prove continuous compliance with integrity controls in place.
Recommendations for HIPAA compliance software in 2019
To help aid continuous compliance and enforce integrity in the process, organizations need to look to HIPAA compliance software rather than native audit and event logs that only yield the data that regulators need to see in modifiable (read not good) reports. Here are some recommendations on what that software should provide in order to meet the technical safeguard obligations for control and integrity of PHI:
- Grant visibility across structured and unstructured data wherever it lives (like file shares and SharePoint Online). When possible, it’s best to seek out a solution that can report and audit across multiple applications (like the Microsoft on-premises and cloud platforms) to reduce the complexity of your IT estate as well as provide a single pane of glass for yourself and auditors.
- Baseline your environment through a discovery and assessment of existing security policies, system configuration settings, location of PHI data, user access rights to that data, and privileged access rights.
- Track and capture user activity against identified PHI data and the access controls that grant those rights, including what was the state of the affected item, what is it now, how it got that way, who did it and who approved it.
- Provide unmodifiable reports of the above information or give convenient access to auditors to access the data directly through the third-party solution.
- Meet HIPAA audit log retention requirements while also easing the burden on storage capacity. NOTE: For Office 365 E3 or below subscribers, audit logs can only be saved for a maximum of 90 days. For customers with Office 365 E5 and Microsoft 365, audit log entries can be retained for a maximum of one year.
Learn more about why PHI data is so valuable, why HIPAA fines are increasing, and how to take measures to prevent healthcare data breaches in this white paper by Osterman Research: Protecting Data in the Healthcare Industry.