Active Directory management is usually straightforward, but on the days when it isn’t, you may need to restore a deleted AD user.
Did you see my previous post, about removing all access, groups and permissions of former employees from servers, groups and AD? That makes it easy to delete objects, but what happens when you make a mistake?
Suppose HR tells you that Jeffrey Lebowski has left the company, and that you should delete his user account. Unaware that there are two people in the company with that name, you delete the first one you find. A half-hour later, a fellow with long hair and a beard comes into your office and sits down.
“I can’t get onto the network, man,” he says. “Why did you delete my account?”
“HR told me to,” you say. “Aren’t you Mr. Lebowski?”
“No. I’m not.”
“You look like the guy whose account I deleted in AD.”
“Let me explain something to you,” he says. “I am not Mr. Lebowski.”
“You look like him,” you say. “Did HR make a mistake?”
“I don’t know. Somebody else is Mr. Lebowski. All I know is that you got the wrong guy and I can’t get on the network now. That, and my rug is ruined.”
“I can’t help with your rug,” you say, “but I’ll try to straighten things out with HR.”
Use case: Restoring a deleted AD object with IT Security Search
Sure enough, you find out from HR that you’ve deleted the wrong Lebowski and you need to restore the account. There’s a rather long way to do it, but IT Security Search makes it much easier.
IT Security Search uses simple, natural search language to help IT administrators quickly locate changes to AD objects, modifications to privileges and inappropriate access to sensitive files and folders. It’s a cost-free feature for Recovery Manager for Active Directory, Change Auditor, Enterprise Reporter, InTrust and Active Roles.
The way IT Security Search integrates with Recovery Manager for Active Directory, you can locate and restore deleted AD objects right through a web interface whether your trying to recover from an accidentally deleted user account or from a far-reaching security breach. You start IT Security Search in your browser and type in a search phrase:
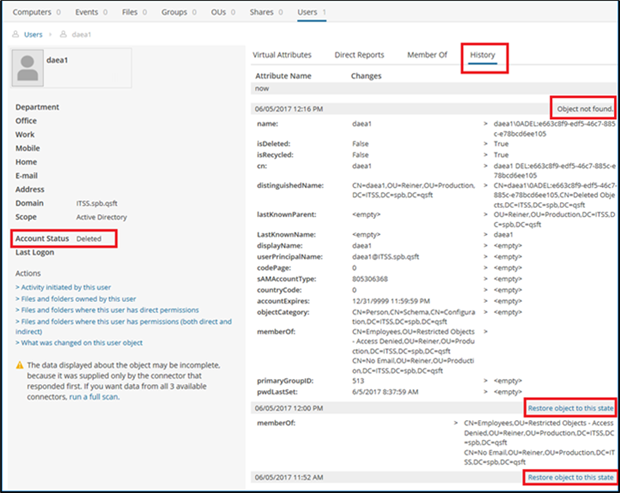
In the search results, you figure out which Lebowski is the one you need to restore and click on it. That reveals the details in his AD object:
Sure enough, Account Status shows “Deleted.” But thanks to IT Security Search, the History tab shows the most recent backups tracked by Recovery Manager for Active Directory. Although the AD object is not found in the most recent backup (you deleted it), you have the option of restoring it from either of the other two backups using the “Restore object to this state” links. If you had changed the object rather than deleting it, you would have the option to restore specific attributes you had modified.
Your turn
Using IT Security Search with Recovery Manager for Active Directory is a powerful way to find, examine and restore data about users, groups, computers and organizational units, even when they’ve been deleted. It’s all the more powerful in combination with the results from Enterprise Reporter, as I described in my previous post, for a deep dive into your entire Windows environment.
IT Security Search is a feature of Recovery Manager for Active Directory, Change Auditor, Enterprise Reporter, InTrust and Active Roles, available for download at no additional cost. Take a 30-day free trial of any or all of those Quest products and try IT Security Search with them.
Look for my next and final post in this series, on how IT Security Search works with Active Roles to supplement native audit details by showing you the actual user who initiated a change to AD.
IT Security Search makes it so easy to restore deleted AD users that maybe you’ll have a few extra minutes to help your co-worker with his rug. After all, it really tied the room together.