Hi, my name's Todd Peterson. I'm a Product Marketing Manager on the Identity Access and Management team at Dell security. And today we're going to talk about where you should start with identity and access management.
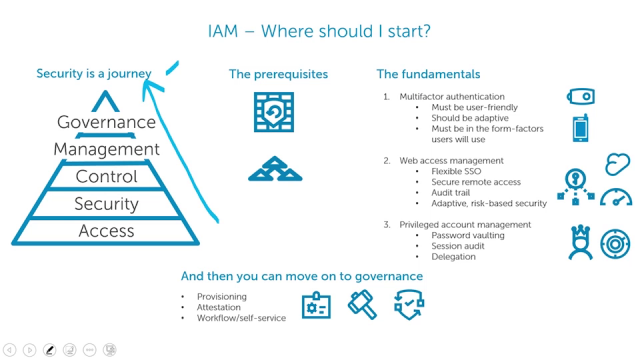
For most people, identity and access management is a lot of things. And it's difficult to know where should I start? And where do I want to go to? And what am I going to accomplish? And how do I get there? So let's start by looking at security as a journey.
If you think about it as a hierarchy where, at the very lower levels of this pyramid, the things that are on the bottom have to be satisfied before you can get to things on the top.
So basically you've got access. Which if access isn't taken care of, you can't accomplish security. If security is not taken care of, you can't have control. If control is not under control, you can't have management.
And ultimately you want to get to a state of governance. And everything you do is guiding you to there. But it's hard to get there. So let's talk about how you can get there and where you should start.
First off, there are some prerequisites. You need to have a next-generation firewall. You need to have a secure way to make sure that the people accessing stuff are getting the right things in the right way. That, you know, bad things aren't coming in. Bad guys are kept out.
And you need to have an enterprise-level directory service. Something similar to Active Directory, maybe another LDAP directory.
There's three areas of identity and access management that we found are kind of the low hanging fruit of idea and access management. The things that if you start there, it'll put you well on the path to achieving what you're ultimately after.
The first is multifactor authentication. That's the things you do to ensure that when somebody logs on, you really do know who they are. That they are who they say they are. So beyond a username and password.
But multifactor authentication has been around for a long time. A lot of people find it difficult and hard to use. So you must choose a solution that's user friendly. It should be adaptive, meaning it should be able to turn on or turn off as needs require, not every single time somebody wants to log on they're required to use the multifactor token.
And it must have the form factors people use. A common multifactor is the little key fob that you push the button on. But people more and more these days are wanting it on their cell phone.
Second is web access management. That would be the things you do to allow people to get to web resources. Whether that's a SaaS application, your own web applications, you know, anything based in the cloud, or on the internet, or that uses a browser as a front-end.
How do you get them to access that? There's lots of solutions for that, but generally those solutions are focused only on one or two types of web access management scenarios.
You want something that does everything. So you want it to give you very flexible single sign-on. Meaning that it will give you single sign-on to the most modern applications as well as to some of your legacy applications.
You want it to give you secure remote access so that people logging in from their own devices, from the road, from wherever, can securely get to the things that you want them to get to without having to jump through a lot of new hoops. You want it to have an audit trail so you know who is accessing what and can adjust accordingly.
And finally, you want to have adaptive, or what we call risk-based security, where the level of enforcement on how strictly you're going to ask for a multifactor token or control what the access, you want that to go up or down depending on the amount of risk associated with the request.
The third area is privileged account management. If you think about the administrative accounts that everybody has, every system, every application, every network device, everything has a privileged account. That's the crown jewels that the bad guys are trying to get a hold of. You need a way to lock those down and to make sure that they don't fall into the wrong hands.
So a couple of things you want to do there. Password vaulting. Make sure that the passwords are not shared. That they're only issued as are necessary. You want session audit. You want to make sure that the activities performed with those privileged credentials are watched, and tracked, and you know what's been done.
And then you want delegation. So for the day-to-day work of your administrators, they're using the rights that they need to do their jobs, but they don't have more rights than they want.
Once you've got these fundamentals taken care of, then you can move on to governance. Which would be things like enterprise provisioning. Making sure that everybody's rights are set up correctly across everything they need to access.
Attestation. That compliance demand for the line of business managers to periodically say, I know who works for me. And I know what they have access to. And I attest that that's appropriate.
And finally workflow, or self-service. Making all those processes to make all that stuff happen, happen as smoothly, and as cleanly, and as easily as possible.
So if you'll start with these fundamentals of identity and access management, then you'll get to governance. So think about what bad guys are trying to do and how these things can help you. People are always trying to steal credentials. If they can get your password, they log on as you. What can they do?
But if you have multifactor in place, somebody steals your
 07:08
07:08
