
The meteoric rise of Microsoft Teams, and the app’s users freely downloading into it, will create more access vulnerabilities for your network. In part 3 of a 7 part series diving in-depth into my 2020 predictions, we’ll explore Microsoft Teams apps, the risks they could pose, and how to safeguard from vulnerable apps.
Microsoft Teams apps and the permission policies in place
First, I love Teams. It’s just so simple to use and our team makes extensive use of its continually updated GIF library to communicate with one another. Beyond the absurdity of my team’s communication style, Teams is an excellent way to share information and communicate within and across Teams, even with our partners! Back in November 2019, Microsoft announced that its new collaboration service reached 20 million daily active users, 7 million of which began using it in just the last 4 months!
One of the ways it’s so valuable, apart from the GIFs, are the apps a user can install in a Team channel to help facilitate the work of that group. I can add in bots, other messaging services, HR and productivity apps and so much more.
However, just like vulnerable apps on our phone can expose our contact list, texts, emails, camera and microphone access, so too can vulnerable or malicious apps in your Teams environment. Think about all the data you have in a Teams channel – access to customer data, marketing plans, IP schematics, and other sensitive data.
Now not just any app can make its way onto the Teams App platform, as Microsoft has controls in place to help screen for malicious apps; but what about those non-malicious apps that have security vulnerabilities left unpatched? There are lots of examples of this happening in any credible app platform.
What’s more alarming is that, by default, all apps are accessible to users to download into their environment, oftentimes with little more than a legitimate email address. And most administrators don’t yet know that this accessibility is on by default!
How to protect your organization from vulnerable Microsoft Teams apps
Microsoft doesn’t leave you hanging in this department, but they don’t make it easy, either. Their first priority is to gain adoption and stickiness of Teams. That’s why the accessibility for all is on by default.
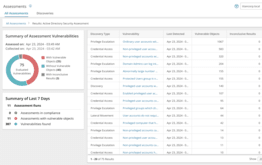
They do provide app permission policies. Here is an overview of what an admin can do:
- As an admin, you can use app permission policies to control what apps are available to Microsoft Teams users in your organization. You can allow or block all apps or specific apps published by Microsoft, third-parties, and your organization. When you block an app, users are unable to install it from the Teams app store.
- You manage app permission policies in the Microsoft Teams admin center. You can apply settings org-wide, use the global (Org-wide default) policy, and create and assign custom policies to individual users or users in a group.
Essentially, you have to know which apps you want to block and which ones you want to authorize. It’s either all or nothing or lots of onsie-twosie restrictions by org, group or user. That’s an overwhelming prospect for administrators just getting their head around Microsoft Teams.
At The Experts Conference, Microsoft Office Apps and Services MVP, Tony Redmond, tackles the topic of managing Microsoft Teams successfully, including how to create governance around the emerging app platform. Watch the recording of his packed session today to learn more about wrapping your head around the app permission policies.



